/ Cybersecurity / Vulnerability Management
From scan to patched.
A scanner that finds 40,000 CVEs is not a program. We close the loop: continuous discovery, exploitability-aware prioritization, automated patching where safe, and tracked SLAs for everything else.
- Continuous discovery across endpoints, servers, cloud, and containers
- Exploitability-first prioritization (KEV, EPSS, in-the-wild signals)
- Automated patch orchestration with safe rollback windows
- SLA tracking with remediation evidence ready for auditors

/ What you get
Everything you need. Nothing you don't.
Continuous discovery
Authenticated and agent-based scanning across endpoints, servers, cloud workloads, containers, and SaaS posture.
Exploitability-first
We don't drown you in CVSS 9.8s. KEV, EPSS, and in-the-wild signals decide what gets patched first.
Automated patching
Where safe, we patch automatically with staged rollouts and one-click rollback. Where not, we open the right ticket.
Compensating controls
Can't patch right now? We'll deploy a virtual patch or detection rule and document the risk acceptance.
Asset truth
One inventory across cloud, on-prem, and remote. No more vulnerabilities found on assets nobody owns.
SLA evidence
Every remediation logged with timestamps and evidence. Hand it to your SOC 2 / ISO auditor unedited.
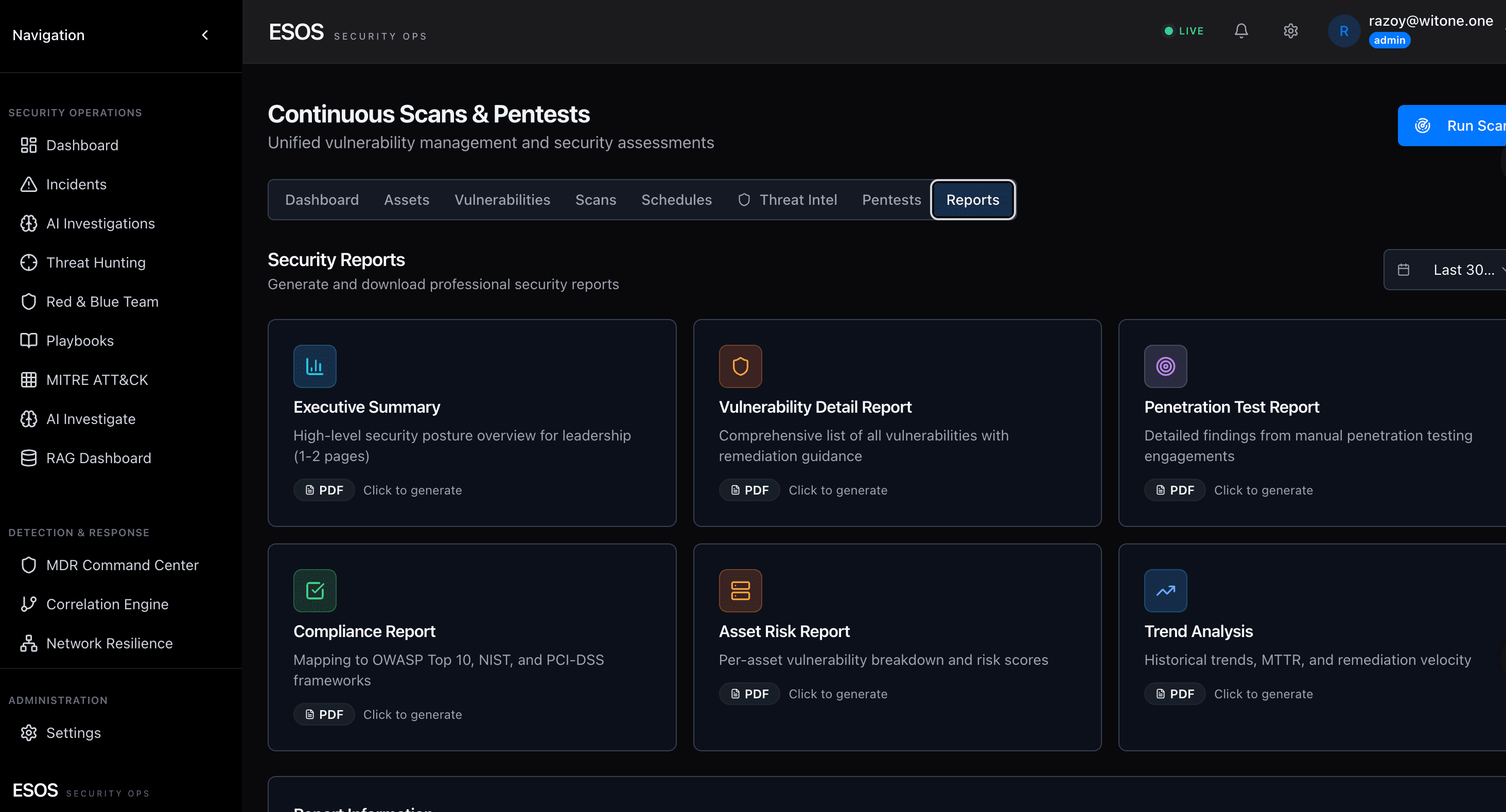
/ Inside the cockpit
Scan output, finally prioritized.
Tenable / Qualys / Rapid7 / Wiz findings reconciled into one queue. CVSS, EPSS, KEV, attack-path reachability, and CMDB criticality combine into one rank. Auto-patch routes through Intune; what's not auto-fixable opens a ticket with owner, SLA, and remediation context.

Ready to run on WIT OS?
Talk to the team about a managed deployment, a pilot, or a custom agent — we typically respond within an hour.
/ FAQ
Frequently asked questions
How is vulnerability management different from a vulnerability scan?
A scan is a point-in-time inventory of weaknesses. Vulnerability management is the ongoing program that prioritizes which to fix, tracks remediation, validates fixes, and reports compliance. WIT ONE's vulnerability management combines continuous scanning, exploit-aware prioritization (EPSS + KEV), and SLA-tracked remediation workflows.
How do you prioritize which vulnerabilities to fix first?
We layer four signals: CVSS severity, EPSS exploit probability, CISA KEV (Known Exploited Vulnerabilities) catalog membership, and asset criticality from your CMDB. A medium-CVSS vuln on a public-facing crown-jewel server with KEV inclusion outranks a critical-CVSS vuln on an isolated lab box.
Do you handle patch deployment?
Yes — we offer Patch Management as a Service. We own the prioritization, deployment coordination, SLA tracking, post-patch validation, and the reporting back to leadership and auditors. Execution runs through your existing tooling (Microsoft Intune, Tanium, BigFix, or similar) or our team — your choice.