/ Cybersecurity / Penetration Testing · Agentic
AI-driven pentest. Not the old way.
This isn't a 2-week consulting engagement that ships a stale PDF six weeks later. WIT OS Agentic Pentest Platform (APT) is an AI-orchestrated security testing engine — it reconnaissances, exploits, captures credentials, maps Active Directory attack paths, and produces both Red Team evidence and Blue Team detection rules in a single coordinated workflow. Full kill chains executed in hours, not weeks. Continuous Breach & Attack Simulation runs in the background indefinitely. Every finding ships with an AI-generated remediation roadmap your team can act on the same day.
- Agentic AI orchestrates recon, exploitation, AD attack paths, credential ops, and lateral movement
- Full kill chain in 2-6 hours · continuous BAS runs 24/7 against the live ATT&CK matrix
- Coordinated Red/Blue: every Red Team finding ships with auto-generated Sigma + KQL + YARA rules
- Every assessment maps to SOC 2, ISO 27001, PCI-DSS, HIPAA, NIST CSF 2.0 — evidence is automatic

/ What you get
Everything you need. Nothing you don't.
Recursive AI orchestrator
An agentic AI engine selects the right tool for the target, interprets results in real time, pivots based on findings, and refines its attack strategy — the same way an elite human operator would, without fatigue or context-switching cost. Reasons over engagement state at every branch point.
Reconnaissance & vulnerability discovery
Subdomain enumeration (Subfinder, Amass, CT logs), network range expansion, cloud asset discovery across AWS/Azure/GCP, API endpoint introspection. 8,000+ Nuclei templates, OpenVAS deep scans, web app testing via Nikto/ZAP/SQLMap/DalFox. Every finding deduplicated, false-positive filtered, ATT&CK-mapped.
Red Team exploitation
Full Metasploit Framework integration with 2,500+ exploit modules. Automated payload selection by target OS, architecture, and AV posture. Meterpreter/shell/PowerShell session management with multi-hop pivoting. Loot collection, screenshot capture, full attack-chain timeline reconstruction.
Active Directory attack paths
BloodHound-python data collection against DCs. Attack-path graph analysis: Kerberoasting, AS-REP roasting, delegation abuse, GPO abuse, DCSync. Computed shortest paths to Domain Admin from any compromised principal. DACL/ACE-level relationship mapping for privilege escalation discovery.
Credential operations
Hash and cleartext dumping via Impacket secretsdump and Mimikatz. Password spraying with intelligent lockout-aware timing. Ticket extraction (TGT/TGS) and Pass-the-Ticket attacks. Hashcat/John integration for offline cracking. Captured credentials encrypted at rest with audit-logged reveal.
SENTINEL Blue Team analysis
For every Red Team finding, an Elite Blue Team Analyst AI generates the defensive counterpart — attack narrative, kill-chain Gantt with break points, critical gaps, credential recommendations, AD hardening guide, and copy-ready Sigma / KQL / YARA / Snort detection rules.
Continuous Breach & Attack Simulation
Beyond on-demand engagements, APT runs continuous BAS using Atomic Red Team and MITRE Caldera. Every customer environment is re-validated against the current ATT&CK matrix daily; delta reporting flags newly successful techniques as soon as defenses drift. Pentesting becomes a continuous signal, not a snapshot.
Coordinated Red/Blue scoring
While the Red Team Orchestrator executes the attack chain, the Blue Team Analyzer monitors customer-side detection signals (Sentinel, CrowdStrike, Defender) in real time and scores detection coverage. Output: adversarial detection score per ATT&CK technique — ✅ detected, ⚠️ logged not alerted, ❌ missed — with Sigma rules to close every miss.
Findings hand-off via WIT OS Flows
Every engagement auto-pushes findings into your existing ITSM (Freshservice, ServiceNow, Jira) with AI-enriched context. Detection rules deploy as Sentinel scheduled analytics. Remediation patches route through Intune. PRs with AI-generated fix code open against GitHub/GitLab. WIT OS Flows owns the workflow.
Audit-ready evidence packs
Every finding maps to applicable compliance controls — SOC 2 CC4/CC6/CC7/CC8, ISO 27001 A.5.7/A.8.8/A.8.29, PCI-DSS 11.3/11.4/6.3, HIPAA §164.308(a)(1)(ii)(A), NIST CSF 2.0 (ID.RA, PR.IP-12, DE.CM-8, RS.MI), GDPR Article 32. Evidence assembles itself; auditors get artifacts on demand.
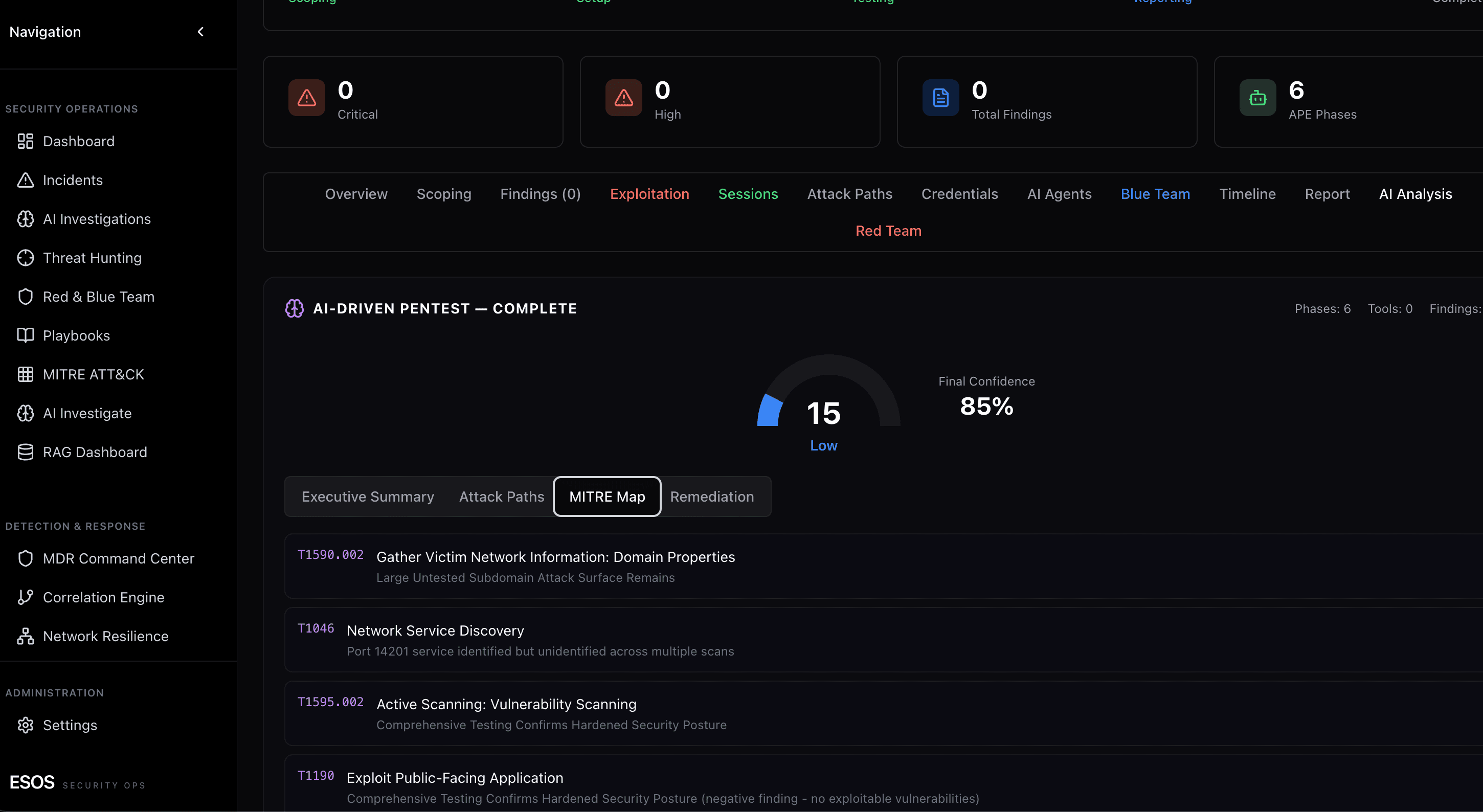
/ Inside the cockpit
Recon → exploit → detect, in one workflow.
Recursive AI orchestrator on top, Red Team execution and SENTINEL Blue Team analysis in coordinated lockstep. Coverage scored per ATT&CK technique; Sigma rules generated for every missed detection; remediation roadmap with effort and owner per task — all in the same operator surface.

Ready to run on WIT OS?
Talk to the team about a managed deployment, a pilot, or a custom agent — we typically respond within an hour.
/ FAQ
Frequently asked questions
How is the Agentic Pentest Platform different from a traditional pen test?
A traditional pen test is a point-in-time consulting engagement: a human runs scans, manually correlates output over days, and ships a PDF weeks later that's stale by the time you read it. The WIT OS Agentic Pentest Platform (APT) is an AI-orchestrated engine — recon, exploitation, AD attack paths, credential ops, and Blue Team detection-rule generation all run in one coordinated workflow. Full kill chains complete in 2-6 hours instead of 2-4 weeks, and continuous BAS runs in the background indefinitely.
What methodology does APT follow?
APT aligns with PTES (Penetration Testing Execution Standard), OWASP Web Security Testing Guide, NIST SP 800-115, and MITRE ATT&CK for adversary emulation — same as a traditional pentest. The difference is execution: an AI orchestrator selects the right tool for the target, interprets results in real time, and pivots based on findings, the way an elite human operator would. Every finding maps to CWE, CVE, and ATT&CK technique IDs.
Does APT replace human pen testers?
No. APT replaces the manual labor — query authoring, tool switching, log parsing, report writing — that consumed 80% of a traditional engagement. Senior human operators stay in the loop on scope definition, rules of engagement, sensitive-asset authorization, and final review of exploitation chains before any destructive action. The AI does the grinding; humans own the judgment.
Do you retest after we fix the findings?
Yes — and because APT runs continuously, retest is a button, not a separate engagement. After your team marks a finding remediated, APT re-validates the same attack chain. Continuous BAS additionally re-runs the entire MITRE ATT&CK matrix daily, so defenses that drift are caught the moment they regress.
What's the difference between APT and a vulnerability scan?
A vulnerability scan inventories weaknesses (CVSS, EPSS, KEV). APT exploits them to prove which are actually reachable and what an attacker could do after initial access — credential capture, AD privilege escalation, lateral movement, data exfiltration paths. For SOC 2 / ISO 27001 / PCI-DSS, scans and pentests are separate compliance requirements; APT satisfies the pentest control while integrating with your scanning program for prioritization.