/ WIT OS · ESOS
Autonomous SOC, operator-grade.
ESOS is the WIT OS security operations orchestrator. Detection, investigation, hunting, and response, fused into a single fabric of MITRE ATT&CK-aware agents working 24/7 alongside your team.
- Sub-3-second mean time to triage across MDR, EDR, and identity
- Autonomous investigation with cited evidence — no opaque verdicts
- MITRE ATT&CK / ATLAS coverage map updated continuously
- Open architecture — extensible across every detection surface

/ What you get
Everything you need. Nothing you don't.
Continuous Detection
Stream-native correlation across endpoint, identity, network, and cloud — every signal mapped to ATT&CK.
Autonomous Investigation
Agents enrich, pivot, and conclude — with citations. Analysts review the case, not the haystack.
Response Playbooks
Pre-approved actions execute at machine speed. Human-in-the-loop where it matters; auto everywhere else.
Threat Hunting
Proactive hypothesis-driven hunts steered by Astute RAG and your environment's normal baseline.
Posture & Coverage
Live ATT&CK coverage map. Find detection gaps before adversaries find them.
Sentinel Guardrails
Every agent action wrapped in Sentinel: DLP, output validation, circuit-breaker, audit trail.
/ Inside the cockpit
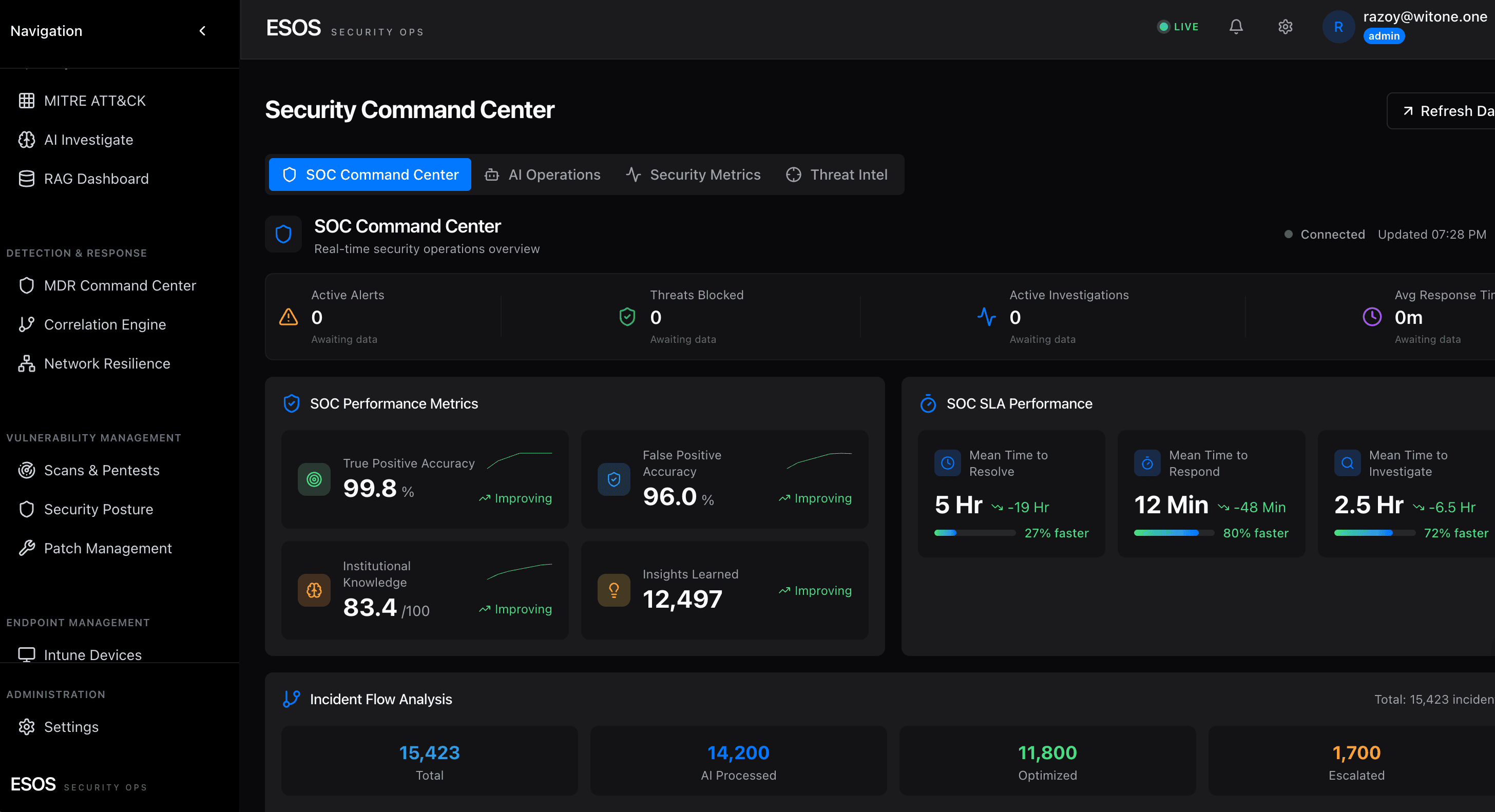
ESOS SOC Command Center · live.
True/false-positive accuracy, SLA performance (MTTR / MTTRespond / MTTI), institutional knowledge growth, and 15K+ incidents flowing through the AI triage funnel — all live.

Ready to run on WIT OS?
Talk to the team about a managed deployment, a pilot, or a custom agent — we typically respond within an hour.
/ FAQ
Frequently asked questions
How is ESOS different from a SIEM?
A SIEM aggregates logs and runs static rules. ESOS is an agent fabric specifically designed for security operations — it ingests SIEM data plus EDR, identity, cloud, and SaaS signals, then reasons over them with MITRE ATT&CK awareness. ESOS produces verdicts and actions; a SIEM produces alerts. We typically run ESOS on top of an existing SIEM.
Does ESOS replace our analysts?
No. ESOS handles commodity alerts and routine investigations so your senior analysts focus on novel threats, threat hunting, and architecture decisions. The ratio of automated-to-human work shifts heavily, but the human role becomes more leveraged, not eliminated.
What metrics does ESOS report on?
MTTR (median + p95), alerts handled by automation vs human, false-positive rate, MITRE ATT&CK coverage, threat hunt yield, time-to-detect for known TTPs, and analyst capacity utilization. Dashboards available in Workspace.